>
Managed IT
>
The IT Maturity Model: How Growing Businesses Scale Technology Without Breaking Operations
The IT Maturity Model: How Growing Businesses Scale Technology Without Breaking Operations
Most businesses don’t struggle because they lack technology—they struggle because their technology doesn’t evolve as they grow. What works for a 10-person team quickly becomes inefficient at 25. At 50, it starts to introduce risk. By the time a company reaches 75 to 100 employees, unmanaged or poorly aligned IT can actively slow growth, create security gaps, and increase operational costs.

This is where the IT Maturity Model becomes critical. Instead of making reactive decisions or implementing tools in isolation, mature organizations follow a structured approach that aligns technology with business outcomes. They understand that IT is not just support—it’s infrastructure for scale.
In this guide, we’ll break down how IT maturity evolves, what risks exist at each stage, and how businesses can move forward with intention instead of reacting under pressure.
What Is the IT Maturity Model?
At its core, the IT Maturity Model measures how effectively an organization uses technology to support its operations, security, and long-term growth. It’s not about how many tools you have—it’s about how well those tools are integrated, managed, and aligned with business goals.
Many organizations assume they are “doing fine” because systems are functioning. But functioning is not the same as optimized. A mature IT environment is one that is predictable, secure, scalable, and strategically aligned with leadership objectives.
As businesses grow, the expectations placed on IT increase. Systems must support more users, more data, more integrations, and higher security requirements. Without a maturity framework, IT decisions become fragmented, and that fragmentation eventually leads to inefficiencies and risk.
The 5 Stages of IT Maturity
1. Reactive IT (Break-Fix Mode)
At the Reactive stage, IT is purely responsive. Issues are addressed only after they occur, and there is little to no planning involved. This is often the starting point for small or growing businesses that have not yet invested in structured IT management.
The challenge with this model is not just inefficiency—it’s unpredictability. Downtime occurs without warning, systems fail without redundancy, and there is no clear understanding of risk exposure. Over time, this creates an environment where technology becomes a liability rather than an asset.
From a business perspective, reactive IT introduces hidden costs. Employees lose time dealing with system issues, leadership lacks visibility into performance, and expenses become inconsistent due to emergency fixes and unplanned upgrades.
Common Indicators:
Frequent downtime or recurring issues
No centralized documentation or standards
IT decisions made under pressure
This is where most organizations begin before realizing the true cost of reactive support:
https://www.kineticcg.com/blog/the-hidden-costs-of-reactive-it-support
2. Basic Managed IT
As organizations grow, they typically move into a managed IT model. At this stage, there is some level of structure—monitoring tools are introduced, help desk systems are implemented, and basic standardization begins to take shape.
This transition improves stability, but it does not fully eliminate reactive behavior. Many businesses in this stage still rely on IT to respond to issues, even if those issues are now tracked and resolved more efficiently. The environment becomes more organized, but not yet optimized.
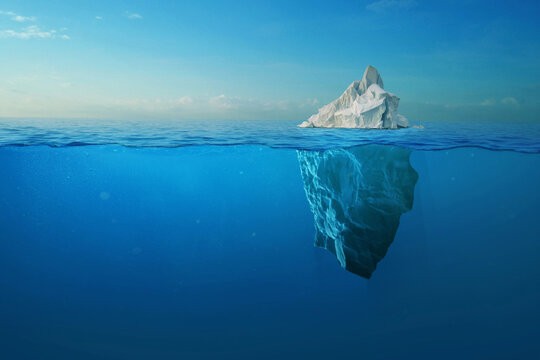
The benefit here is consistency. Systems are more reliable, support is more accessible, and costs begin to stabilize. However, without a proactive strategy, underlying risks and inefficiencies still exist beneath the surface.
Supporting Indicators:
Tickets are tracked and resolved systematically
Monitoring tools provide basic visibility
Reduced—but not eliminated—downtime
3. Proactive IT Management
At the Proactive stage, IT begins to shift from reaction to prevention. This is one of the most important transitions in the maturity curve because it introduces predictability into the environment.
Instead of waiting for failures, systems are continuously monitored, updated, and optimized. Automated patching ensures vulnerabilities are addressed quickly, while monitoring tools detect anomalies before they escalate into major incidents. This significantly reduces downtime and improves overall system performance.
Cybersecurity also becomes a central focus at this stage. Businesses begin implementing layered protections such as endpoint detection and response (EDR), multi-factor authentication (MFA), and backup and disaster recovery solutions. These controls dramatically reduce both the likelihood and impact of cyber incidents.
The real shift here is confidence. Leadership can begin to rely on technology as a stable foundation rather than a constant concern. This stability is what enables growth.
Supporting Indicators:
Significant reduction in recurring issues
Faster detection and response to threats
Increased visibility into system health
This aligns closely with Kinetic’s ProTek model—focused on stability and protection.
4. Strategic IT Alignment
Once IT becomes stable and proactive, the next step is alignment with business strategy. At this stage, technology decisions are no longer made in isolation—they are directly tied to organizational goals.
This means IT budgets are planned in advance, infrastructure decisions are aligned with growth projections, and leadership teams collaborate with IT to drive outcomes. Instead of asking, “How do we fix this issue?” the conversation shifts to, “How can technology help us scale?”
Strategic alignment transforms IT from a cost center into a value driver. Businesses can expand more confidently, adopt new technologies more effectively, and respond to market changes with greater agility.
Supporting Indicators:
IT roadmap aligned with business goals
Predictable budgeting and forecasting
Reduced reliance on reactive decision-making
5. Optimized / Innovation-Driven IT
At the highest level of maturity, IT becomes a competitive advantage. Organizations in this stage are not just maintaining systems—they are continuously optimizing and innovating.
Automation plays a significant role here, reducing manual effort and increasing efficiency across operations. Data analytics provides insight into performance, enabling better decision-making at every level of the business. Emerging technologies such as AI and advanced integrations are leveraged strategically, not experimentally.
This stage is characterized by continuous improvement. Systems are regularly evaluated, processes are refined, and technology is used to unlock new opportunities rather than simply support existing ones.
Supporting Indicators:
High operational efficiency with minimal downtime
Advanced automation and data-driven insights
Strong, continuously improving security posture
IT Maturity Model Overview
Stage | Focus | Risk Level | Business Impact |
|---|---|---|---|
Reactive | Fix issues | Very High | Frequent disruption |
Managed | Stabilize | High | Moderate reliability |
Proactive | Prevent | Medium | Strong performance |
Strategic | Align | Low | Scalable growth |
Optimized | Innovate | Very Low | Competitive advantage |
Why Businesses Get Stuck
Many organizations plateau between managed and proactive IT. This happens because systems appear to be “working,” which creates a false sense of stability.
Without clear visibility into risk, leadership often delays further investment. At the same time, internal IT resources or vendors may lack the strategic perspective needed to move the business forward. The result is an environment that is functional—but fragile.
Over time, this gap becomes more apparent. Growth introduces new demands, security threats increase, and the limitations of the current IT model begin to surface.
The Cost of Staying Immature
Remaining in a lower stage of IT maturity has compounding consequences. Downtime becomes more expensive as operations scale. Security risks increase as threat landscapes evolve. And inefficiencies multiply as systems become more complex.
These costs are not always immediately visible, but they impact productivity, employee experience, and ultimately revenue.
For a deeper breakdown of how downtime affects business operations:
https://www.kineticcg.com/blog/the-true-cost-of-it-downtime-why-businesses-can’t-afford-to-wait-and-fix-anymore
How to Advance Your IT Maturity
Improving IT maturity is not about a single upgrade—it’s about a structured progression. Businesses must first understand where they are, then take deliberate steps toward improvement.
This typically begins with a comprehensive assessment of systems, security, and workflows. From there, organizations can standardize their environment, implement proactive tools, and build a roadmap that aligns technology with business goals.
The most important factor is consistency. Maturity is not achieved through isolated improvements—it is built through ongoing optimization and strategic planning.
Key Steps:
Assess current systems and risks
Standardize infrastructure and processes
Implement proactive monitoring and security
Develop a forward-looking IT roadmap
Partner with a strategic IT provider
Kinetic Insight
At Kinetic Consulting Group, we help businesses move beyond reactive IT and into structured, scalable environments.
Our approach is designed to guide organizations through each stage of maturity:
ProTek establishes stability, security, and proactive management
Kore+ aligns technology with long-term business strategy
The goal is not just better IT—it’s better business outcomes driven by technology.
Key Takeaway
Technology should scale with your business—not hold it back.
If your IT strategy hasn’t evolved alongside your growth, there is a strong likelihood that inefficiencies and risks are already building beneath the surface. The organizations that succeed long-term are the ones that treat IT as a strategic function, not just a support service.