The Hidden Risk in “Fully Managed” IT: Why Most MSPs Fail at True Accountability
In today’s technology landscape, outsourcing IT is no longer a tactical decision, it is a strategic one. Businesses are not simply looking for someone to fix issues, they are looking for stability, security, and a foundation that enables growth. The Managed Service Provider model was originally designed to meet this need, offering predictable support and centralized management. However, as technology environments have become more complex and threat landscapes more aggressive, the traditional MSP model has failed to evolve at the same pace.

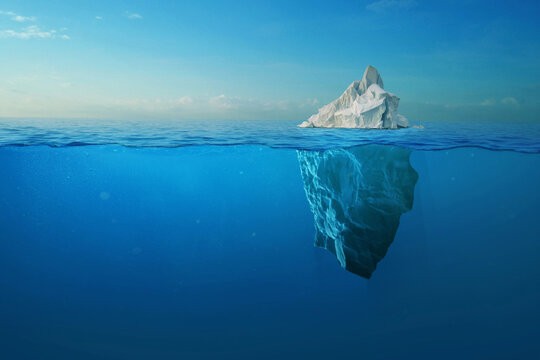
What most businesses believe they are buying is peace of mind. What they are often receiving is operational support without true ownership. This distinction is subtle, but it is where the majority of modern IT risk originates.
Across private equity firms, law practices, and manufacturing organizations, the same pattern continues to emerge. Companies believe their environments are managed, yet when tested under pressure, whether through a cyber incident, system failure, or rapid growth requirement, the cracks begin to show. These failures are rarely due to a lack of tools or effort. They are the result of a fundamental misalignment between activity and accountability.
The Illusion of “Fully Managed”
The term “fully managed” has become one of the most overused phrases in the IT services industry. It suggests completeness, control, and continuity. In practice, most MSP agreements are structured around service activity, not business outcomes.
Service level agreements typically emphasize:
Ticket response times
Resolution speed
Device coverage
Helpdesk availability
While these metrics create the appearance of performance, they do not measure what actually matters to the business. They do not measure downtime impact, security effectiveness, or operational efficiency.
This is the core of the illusion.
A business can have fast response times and still experience recurring issues. It can have a modern tool stack and still be vulnerable to breach. It can have 24/7 support and still suffer from systemic inefficiencies that slow growth. These gaps are not theoretical. They are a direct extension of the reactive IT model, which we explored in detail in our breakdown of the hidden costs of reactive IT support, where short term fixes consistently create long term operational drag.
Where Expectations Diverge from Reality
Area | Business Expectation | Typical MSP Delivery |
|---|---|---|
Cybersecurity | Prevention and risk reduction | Alerting and response |
Infrastructure | Scalable, optimized systems | Functional but aging environments |
Strategy | Alignment with business growth | Tool recommendations |
Accountability | Ownership of outcomes | Ownership of tasks |
This gap between expectation and delivery is not always visible day to day. It becomes apparent during moments of stress, when systems fail, threats materialize, or the business attempts to scale.
The True Cost of Reactive IT
Downtime is often used as the primary metric for evaluating IT performance, but it only represents the most visible form of failure. The deeper cost of reactive IT is cumulative and often hidden within daily operations.
As outlined in our analysis of the true cost of IT downtime, the financial impact of a single outage can be substantial, but the ongoing inefficiencies caused by poorly managed environments are often far more damaging over time.
Organizations operating in reactive IT environments typically experience:
Repeated minor disruptions that erode productivity
Redundant tools that increase cost without increasing capability
Delayed decision making due to unreliable systems
Increased employee frustration and turnover
These factors create a continuous drag on performance.
Quantifying the Impact
Impact Category | Business Effect | Estimated Impact |
|---|---|---|
Unplanned Downtime | Lost revenue, halted operations | $10K to $300K+ per hour |
Security Incidents | Data loss, legal exposure | $4.45M average breach cost |
Productivity Loss | Inefficient workflows | 20% to 30% reduction |
Tool Sprawl | Redundant systems | 15% to 25% wasted spend |
The key takeaway is that reactive IT is not simply inefficient, it is expensive in ways that are not immediately visible on a balance sheet.
Why Accountability Breaks Down
At the center of the issue is accountability. The traditional MSP model distributes responsibility across tools, processes, and teams, but rarely consolidates ownership of outcomes.
When incidents occur, responses are often framed around process validation rather than business impact:
Alerts were generated
Systems were functioning
Procedures were followed
While technically accurate, these responses do not address the fundamental question, why was the business exposed in the first place?
This is the difference between operational IT and strategic IT.
Most providers are structured around managing individual components of the environment. They manage endpoints, backups, security tools, and networks as separate functions. What is often missing is ownership of how these components work together to produce a secure and efficient system.
This is where the concept of ROI becomes critical. As explored in the real ROI of managed IT services, value is not created by deploying tools, it is created by aligning those tools with measurable business outcomes.
Without this alignment, businesses are effectively renting infrastructure without receiving the benefits of true management.
The Fragmentation Problem in Modern IT
One of the most significant risks in today’s IT environments is fragmentation. Businesses invest in multiple layers of protection and infrastructure, but those layers often operate independently.
A typical environment may include:
Endpoint protection
EDR solutions
Backup systems
Identity management platforms
Cloud infrastructure
Each of these components may function correctly on its own. The problem arises when there is no unified strategy governing how they interact.
This creates what appears to be a strong defense but is, in reality, a loosely connected set of tools. This challenge is explored in depth in our analysis of the visibility gap in modern IT, where lack of integration leads to failure at critical moments.
The result is a fragmented defense model where:
Alerts are generated but not correlated
Threats move laterally across systems
Backups exist but are not validated against real scenarios
Access controls are implemented but not continuously reviewed
This fragmentation creates a dangerous dynamic, perceived security without actual resilience.
The Danger of the Security Illusion
Perhaps the most critical issue facing businesses today is not a lack of security tools, but a false sense of security.
Organizations often believe they are protected because they have implemented industry standard controls. However, without continuous validation and integration, these controls can create blind spots.
This phenomenon is explored in the security illusion, where businesses assume coverage without verifying effectiveness.
The consequences of this illusion are significant:
Delayed detection of threats
Incomplete incident response
Overconfidence in recovery capabilities
Increased exposure during targeted attacks
Security is not a checklist. It is a continuous process that requires oversight, testing, and adaptation.
From Operational IT to Strategic IT
The transition from reactive, tool based IT management to outcome driven IT leadership is best understood through maturity progression.
As outlined in the IT maturity model for growing businesses, organizations move through several stages before achieving true alignment between technology and business objectives.
IT Maturity Progression
Stage | Characteristics | Risk Level |
|---|---|---|
Reactive | Issue driven, minimal planning | High |
Managed | Structured support, tool deployment | Moderate |
Proactive | Monitoring, optimization | Lower |
Strategic | Business aligned IT leadership | Minimal |
Most MSP relationships operate between the managed and proactive stages. Very few deliver true strategic alignment.
The difference lies in ownership. Strategic IT is not about maintaining systems, it is about enabling outcomes.
The Kinetic Approach: Strategy. Security. Scalability.
At Kinetic Consulting Group, the philosophy is built around a simple but critical principle, IT must be accountable to the business.
Strategy ensures that every technology decision supports long term growth and operational efficiency.
Security ensures continuous risk identification, mitigation, and validation.
Scalability ensures that systems evolve with the business without introducing instability or complexity.
This model shifts IT from a reactive support function to a proactive driver of performance.
It also reinforces a broader truth that has been consistent across every analysis we have published, businesses that align IT with measurable outcomes consistently outperform those that treat it as a background function.
Final Takeaway
The question businesses should be asking is no longer whether their IT is managed. It is whether it is truly owned.
A provider that manages tickets is not the same as a provider that manages risk. A provider that maintains systems is not the same as one that enables growth.
The gap between these models is where most businesses either struggle or scale.
Those that continue to operate within traditional MSP frameworks will encounter increasing inefficiencies, rising security exposure, and limitations on growth. Those that demand accountability, integration, and outcome driven performance will position themselves for long term resilience.