More Tools, More Risk: The Operational Failure Behind Modern IT Stacks
Over the last decade, businesses have aggressively adopted new technology to improve productivity, security, and scalability. From cloud platforms and collaboration suites to cybersecurity stacks and automation tools, the modern IT environment is richer and more capable than ever before. But there is a growing problem that most organizations fail to recognize until it is too late. More tools do not automatically mean better outcomes. In fact, the opposite is often true.

Tool sprawl, the uncontrolled expansion of IT and security solutions across an organization, is quietly becoming one of the biggest operational and cybersecurity risks facing businesses today. What begins as a strategic effort to strengthen infrastructure often evolves into a fragmented ecosystem where visibility is lost, accountability is diluted, and risk increases in ways leadership never intended.
At Kinetic Consulting Group, we consistently see organizations investing heavily in technology, yet operating in environments that are more vulnerable, not less.
This is not a failure of technology. It is a failure of strategy.
Strategy. Security. Scalability.
What Is Tool Sprawl and Why Does It Happen?
Tool sprawl occurs when businesses continuously add new technologies without a centralized strategy for integration, visibility, and governance. Each department, vendor, or initiative introduces its own tools, often solving a specific problem but creating a larger systemic issue.
This typically happens for three reasons.
First, reactive decision making. Organizations adopt tools in response to immediate challenges, such as adding endpoint protection after a scare or deploying a new SaaS platform to improve collaboration. These decisions are often made in isolation.
Second, vendor-driven expansion. Many IT providers and software vendors encourage layering additional tools rather than optimizing existing ones. This leads to overlapping functionality and redundant systems.
Third, lack of centralized ownership. Without a clear technology strategy, different stakeholders make independent decisions, resulting in a fragmented environment.
The result is an ecosystem where tools exist, but they do not work together.
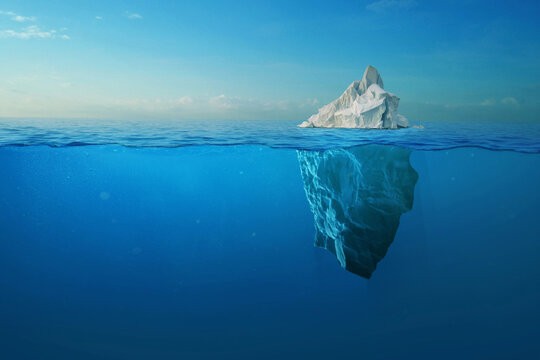
The Illusion of Security Through Volume
One of the most dangerous outcomes of tool sprawl is the false sense of security it creates.
Organizations often believe that having more security tools means they are better protected. However, security is not defined by the number of solutions in place, but by how effectively they are integrated, monitored, and managed.
Consider how this connects to our previous insights in
https://www.kineticcg.com/blog/the-security-illusion-why-most-businesses-think-they%E2%80%99re-protected-until-they%E2%80%99re-not
Many businesses operate under the assumption that their stack is “complete” because it includes antivirus, EDR, backup, email security, and compliance tools. But without alignment between these systems, gaps inevitably form.
These gaps are where attackers operate.
Where Tool Sprawl Creates Real Risk
1. Visibility Gaps Across Systems
When multiple tools operate independently, there is no single source of truth. Alerts are scattered, logs are siloed, and correlations are missed.
This directly ties into the challenges outlined in
https://www.kineticcg.com/blog/the-visibility-gap-in-modern-it-why-most-security-stacks-fail-when-it-matters-most
Without unified visibility, critical signals are lost in noise. Security teams cannot see the full picture, which delays detection and response.
2. Overlapping Functionality and Redundancy
Many organizations unknowingly pay for multiple tools that perform similar functions.
Function | Tool A | Tool B | Result |
|---|---|---|---|
Endpoint Protection | Antivirus | EDR | Partial overlap |
File Storage | OneDrive | Egnyte | Data fragmentation |
Monitoring | RMM Alerts | Security Alerts | Alert fatigue |
This redundancy does not improve security. It creates confusion about which system is authoritative.
For a deeper breakdown of how overlapping tools impact effectiveness, refer to
https://www.kineticcg.com/blog/antivirus-vs-edr-which-is-better-for-your-business
3. Increased Attack Surface
Every additional tool introduces new entry points.
Each platform has its own:
Authentication model
API integrations
Configuration requirements
Potential vulnerabilities
When these systems are not tightly controlled, the attack surface expands significantly.
This is especially relevant in environments heavily reliant on SaaS platforms, as discussed in
https://www.kineticcg.com/blog/the-hidden-complexity-of-microsoft-365-why-most-businesses-are-misconfigured-by-default
Misconfigurations across multiple tools compound risk exponentially.
4. Alert Fatigue and Missed Threats
More tools generate more alerts.
But more alerts do not mean better detection. They often lead to alert fatigue, where teams become desensitized and begin ignoring or deprioritizing notifications.
When everything is urgent, nothing is.
This is one of the core reasons why breaches often go undetected for extended periods, even in organizations with robust toolsets.
5. Operational Inefficiency
Tool sprawl does not just impact security. It affects day-to-day operations.
Teams spend more time:
Managing multiple dashboards
Reconciling conflicting data
Training staff on different platforms
Troubleshooting integration issues
This inefficiency directly impacts productivity and increases costs.
As explored in
https://www.kineticcg.com/blog/the-real-roi-of-managed-it-services-for-growing-businesses
technology should reduce friction, not create it.
The Business Impact of Tool Sprawl
The consequences of tool sprawl extend beyond IT.
They affect the entire business.
Impact Area | Result |
|---|---|
Financial | Increased licensing costs, redundant spending |
Security | Higher breach probability due to gaps |
Compliance | Difficulty proving control and audit readiness |
Productivity | Slower operations and reduced efficiency |
Scalability | Complex environments that cannot scale cleanly |
Organizations often do not realize these impacts until they experience a major disruption.
This mirrors the broader issue highlighted in
https://www.kineticcg.com/blog/the-true-cost-of-it-downtime-why-businesses-can%E2%80%99t-afford-to-wait-and-fix-anymore
where hidden inefficiencies eventually translate into measurable business loss.
Why Most MSPs Fail to Address Tool Sprawl
Many managed service providers contribute to this problem rather than solving it.
The reason is simple.
It is easier to add tools than to optimize systems.
True optimization requires:
Deep architectural understanding
Cross-platform expertise
Continuous monitoring and refinement
Strategic alignment with business goals
Most MSPs operate reactively, layering solutions instead of consolidating them.
This is part of a broader issue discussed in
https://www.kineticcg.com/blog/the-hidden-risk-in-%E2%80%9Cfully-managed%E2%80%9D-it-why-most-msps-fail-at-true-accountability
where accountability is replaced with surface-level management.
The Shift From Tool-Centric to Strategy-Centric IT
The solution to tool sprawl is not fewer tools.
It is better strategy.
Organizations need to shift from a tool-centric mindset to a strategy-centric approach where every technology decision is aligned with:
Business objectives
Security requirements
Operational efficiency
Long-term scalability
This requires a structured framework.
The Kinetic Approach to Eliminating Tool Sprawl
At Kinetic Consulting Group, we approach this challenge through three core principles.
1. Rationalization
We evaluate every tool in the environment and answer critical questions:
What function does it serve
Is it redundant
Is it fully utilized
Does it integrate effectively
The goal is not to remove tools arbitrarily, but to ensure every tool has a defined purpose.
2. Consolidation
Where overlap exists, we consolidate functionality into fewer, more powerful platforms.
This reduces:
Complexity
Cost
Risk
While improving:
Visibility
Control
Efficiency
3. Integration and Visibility
We ensure that remaining tools are:
Properly integrated
Centrally monitored
Aligned within a unified framework
This eliminates blind spots and creates a cohesive security and operational posture.
What a Streamlined IT Environment Looks Like
A well-structured environment is not defined by how many tools it has, but by how effectively they work together.
Characteristic | Fragmented Environment | Optimized Environment |
|---|---|---|
Visibility | Siloed dashboards | Centralized monitoring |
Security | Reactive | Proactive and layered |
Cost | Redundant | Optimized and predictable |
Operations | Complex | Streamlined |
Scalability | Limited | Built for growth |
This transformation is what enables businesses to move from reactive IT to strategic IT.
How to Identify If Your Business Has a Tool Sprawl Problem
Most organizations already have this issue. The question is whether they recognize it.
Here are common indicators:
Multiple tools performing similar functions
Lack of clarity on which system is authoritative
Frequent alert overload with little actionable insight
Difficulty passing compliance audits
Rising IT costs without measurable improvement
Slow response times to incidents
If these sound familiar, the problem is already impacting your business.
The Cost of Doing Nothing
Ignoring tool sprawl does not maintain the status quo.
It makes the problem worse.
As organizations grow, they continue adding tools, increasing complexity, and expanding risk. Eventually, this leads to:
Security incidents
Operational breakdowns
Compliance failures
Financial loss
This aligns with the broader trend seen in modern IT environments where complexity becomes the primary risk factor.
Final Thoughts: Complexity Is the New Vulnerability
The modern threat landscape is not just targeting weaknesses in software.
It is targeting weaknesses in architecture.
Tool sprawl creates complexity. Complexity creates gaps. Gaps create risk.
Businesses that fail to address this will continue investing in technology while becoming less secure and less efficient.
Those that take a strategic approach will gain a significant advantage.
They will operate with clarity, control, and confidence.
Strategy. Security. Scalability.