When IT Stops Being an Enabler and Starts Becoming a Liability
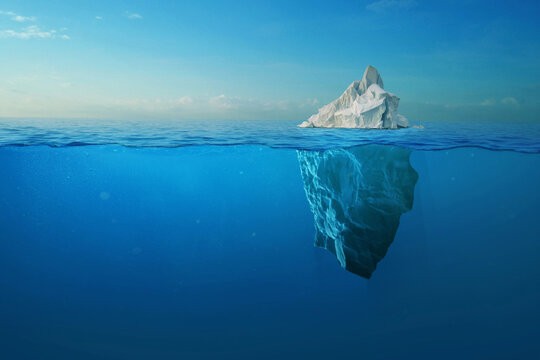
Technology is supposed to accelerate growth, not constrain it. Yet for many small to mid-sized businesses, especially those operating between 15 and 50 endpoints, IT quietly transitions from a strategic advantage into an operational liability. The shift is subtle at first. Systems still function, users still log in, tickets still get resolved. But beneath the surface, inefficiencies compound, risks accumulate, and scalability begins to erode.

At Kinetic Consulting Group, we consistently see this inflection point appear not when businesses are struggling, but when they are growing. Growth amplifies everything, including the weaknesses embedded within your IT environment. If those weaknesses are not addressed proactively, they become the bottleneck that limits how far and how fast your business can scale.
This is where the difference between reactive IT and strategic IT becomes critical.
The Illusion of “Working” Technology
Most organizations assume their IT is in a good place because nothing appears broken. Systems are online, employees are productive, and there are no major outages. However, “working” does not mean optimized, secure, or scalable.
This illusion is one of the most dangerous states a business can operate in.
In many environments, technology debt accumulates silently. Legacy configurations remain untouched, security tools are deployed but not tuned, and integrations between systems become increasingly fragile. Over time, this creates an environment where everything technically functions, but nothing operates efficiently.
Many businesses only recognize this gap after experiencing a security event or operational failure, reinforcing the broader issue that perceived protection often does not reflect reality.
🔗 https://www.kineticcg.com/blog/the-security-illusion-why-most-businesses-think-they%E2%80%99re-protected-until-they%E2%80%99re-not
The reality is simple: if your IT strategy has not evolved alongside your business, it is already outdated.
The Compounding Effect of IT Complexity
As organizations grow, they naturally adopt more tools. Collaboration platforms like Microsoft 365, endpoint protection platforms, backup solutions, line-of-business applications, and industry-specific software all become part of the stack.
Individually, each tool may solve a specific problem. Collectively, they introduce complexity.
This complexity creates three major challenges:
1. Fragmented Visibility
Different tools operate in silos. Security alerts live in one platform, backups in another, user management somewhere else. Without centralized visibility, identifying risk becomes difficult and response times increase.
2. Operational Inefficiency
Teams spend more time managing tools than leveraging them. Instead of enabling productivity, IT becomes a maintenance function.
3. Increased Risk Surface
Every new system introduces another potential entry point for attackers. Without proper integration and oversight, these gaps become exploitable.
As environments expand, organizations often discover that more tools do not equate to better outcomes, but instead introduce operational failure points that are difficult to manage at scale.
🔗 https://www.kineticcg.com/blog/more-tools-more-risk-the-operational-failure-behind-modern-it-stacks
Why Growth Breaks IT Before It Breaks the Business
One of the most overlooked realities in business is that IT infrastructure often fails before revenue, operations, or customer demand show signs of strain.
Growth introduces pressure in several key areas:
Growth Factor | IT Impact | Business Risk |
|---|---|---|
Increased headcount | User provisioning complexity | Security gaps, onboarding delays |
More data | Storage and backup strain | Data loss, compliance exposure |
Remote work expansion | Endpoint and identity management challenges | Unauthorized access, breaches |
System dependencies | Application interconnectivity increases | Downtime cascade failures |
As these pressures increase, IT environments that were once sufficient begin to show cracks, often slowing down operations long before leadership understands the root cause.
🔗 https://www.kineticcg.com/blog/the-it-bottleneck-nobody-plans-for-why-growth-breaks-your-technology-before-it-breaks-your-business
The Hidden Cost of Reactive IT
Reactive IT is one of the most expensive operational models a business can adopt, even if it appears cost-effective on the surface.
Instead of preventing issues, reactive environments respond to them after they occur. This leads to increased downtime, higher incident resolution costs, loss of employee productivity, and greater exposure to security events.
More importantly, reactive IT prevents businesses from planning strategically. Every decision becomes urgent rather than intentional.
Over time, this model introduces compounding inefficiencies that directly impact both operational performance and long-term profitability.
🔗 https://www.kineticcg.com/blog/the-hidden-costs-of-reactive-it-support
The key takeaway is that reactive IT does not just cost more financially, it limits your ability to scale confidently.
Security as a Growth Dependency, Not a Feature
Cybersecurity is often treated as a separate initiative, something layered on top of existing infrastructure. In reality, security must be embedded into the foundation of your IT strategy.
Modern threats target identity, endpoints, and backups simultaneously. The rise of identity-based attacks, especially within platforms like Microsoft Azure Active Directory, has shifted the focus from perimeter defense to internal control.
Recent attack patterns demonstrate that adversaries are no longer just attempting to gain access, they are targeting persistence, privilege escalation, and the destruction of recovery mechanisms. This evolution has made backup integrity and identity security central components of any resilient IT strategy.
🔗 https://www.kineticcg.com/blog/when-backup-becomes-the-target-what-the-april-2026-veeam-exploit-campaign-reveals-about-the-next-evolution-of-ransomware
This shift reinforces a critical point: if your IT environment is not architected with security in mind, growth only increases your exposure.
The Role of IT Maturity in Scalable Growth
Not all IT environments are created equal. Maturity is what separates organizations that scale smoothly from those that encounter constant friction.
A mature IT environment is defined by standardized processes, centralized visibility, integrated security controls, predictable performance, and proactive monitoring and optimization.
Organizations that invest in IT maturity frameworks are better equipped to align technology with business growth, reducing friction and improving long-term outcomes.
🔗 https://www.kineticcg.com/blog/the-it-maturity-model-how-growing-businesses-scale-technology-without-breaking-operations
Organizations operating at higher levels of IT maturity experience fewer disruptions, lower risk, and greater operational efficiency. More importantly, they are positioned to leverage technology as a competitive advantage rather than a constraint.
What Strategic IT Actually Looks Like
Strategic IT is not defined by the tools you use. It is defined by how those tools are aligned with your business objectives.
At Kinetic Consulting Group, we anchor this approach around three core principles:
Strategy
Technology decisions must be driven by business outcomes, not vendor capabilities. This includes roadmap planning, lifecycle management, and aligning IT investments with growth initiatives.
Security
Security is embedded across every layer of the environment, from endpoint protection to identity management and backup integrity. It is not an add-on, it is foundational.
Scalability
Systems must be designed to grow with the business. This includes automation, standardized configurations, and infrastructure that can adapt without requiring constant reinvention.
This is the framework behind everything we build, ensuring that IT remains an enabler rather than becoming a liability.
The Inflection Point: When to Rethink Your IT Strategy
Most businesses do not proactively decide to overhaul their IT strategy. Instead, they are forced to react when something breaks.
However, there are clear indicators that your environment is approaching a breaking point:
Increasing frequency of support tickets
Slower onboarding of new employees
Lack of visibility into security events
Difficulty integrating new systems or tools
Growing reliance on manual processes
If any of these conditions exist, your IT environment is already under strain.
The goal is not to wait for failure. The goal is to recognize the signals early and transition toward a strategic model before those risks materialize into real-world impact.
Kinetic Insight
The biggest mistake growing businesses make is assuming their IT environment will scale naturally alongside them. It will not.
Technology does not evolve on its own. Without intentional design, it becomes fragmented, inefficient, and vulnerable. The organizations that succeed long-term are the ones that treat IT as a strategic function, not a support service.
At Kinetic Consulting Group, we do not just manage IT environments. We architect them for growth, security, and long-term scalability.
Strategy. Security. Scalability.
Key Takeaway
If your IT “works,” that is not enough.
The real question is whether it is optimized, secure, and scalable for where your business is going next. Because the moment your IT becomes a limitation, it is no longer supporting your growth, it is defining its ceiling.